-
How Neural Networks Detect Watermarks
Neural networks detect invisible watermarks in images, video, and audio by analyzing frequency features and training robust models that resist edits.
-
Neural Audio Watermarking: Attacks and Defenses
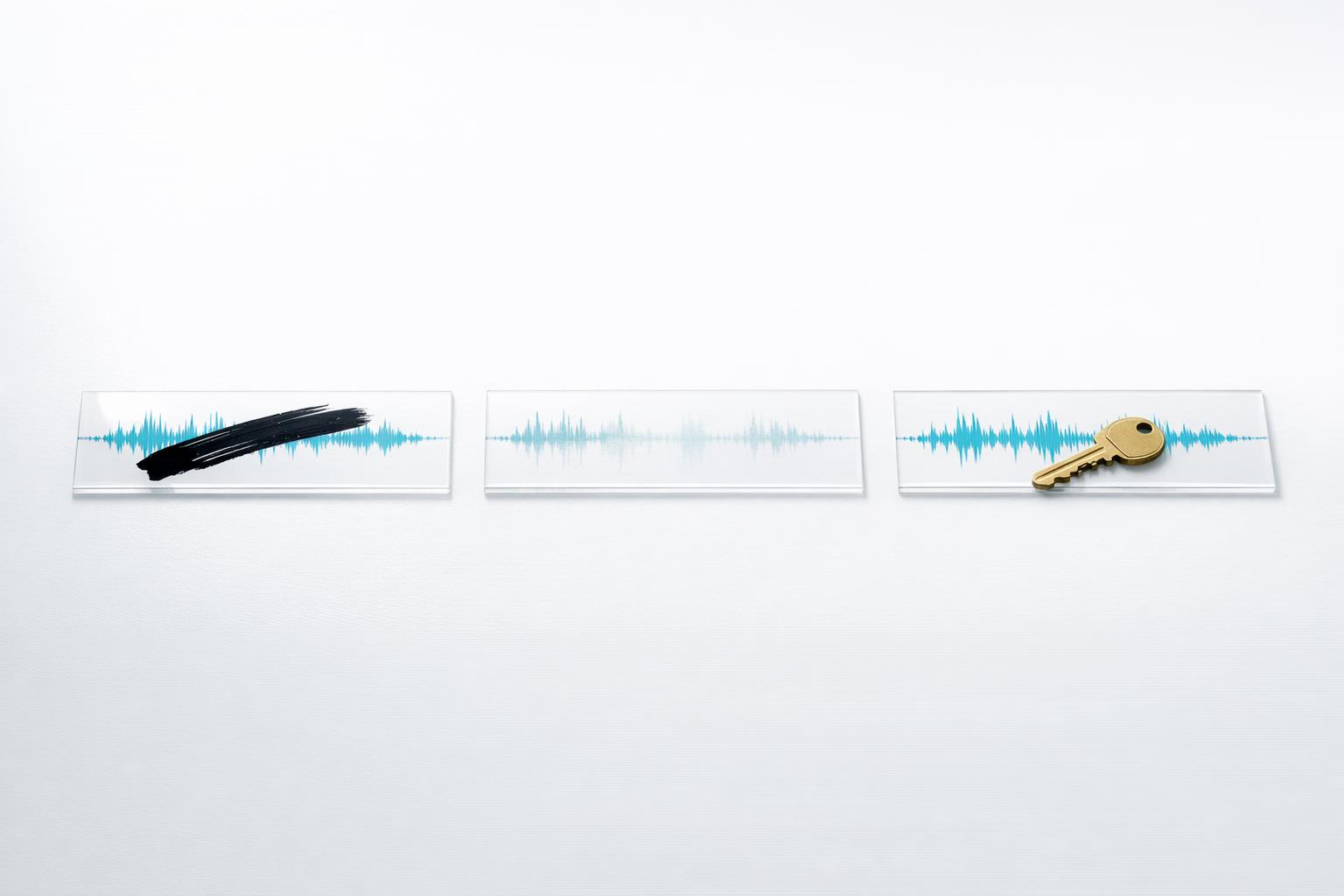
Three neural audio watermarking systems are critically vulnerable: overwriting attacks succeed nearly 100% and neural codecs can erase watermarks—key-based defenses are needed.
-
Perceptual Watermarking in Digital Piracy Prevention
Invisible perceptual watermarks embed resilient ownership signals into images, video, and audio—surviving compression, cropping, and AI edits while enabling blockchain verification.
-
Watermark Robustness: AI Techniques Explained

Explains how GANs, diffusion models, error-correcting codes and adversarial training create invisible, durable watermarks that resist edits, regeneration and attacks.
-
How Cloud Audio Watermarking Protects IP

Invisible cloud audio watermarks embed tamper-resistant IDs in recordings to trace leaks, deter piracy, and prove ownership.
-
Future of Energy-Efficient Audio Watermarking
Compare time- and frequency-domain audio watermarking, energy trade-offs, blind extraction trends, wavelet methods, and enterprise-scale solutions.
-
Blockchain and Cross-Platform Audio Watermarking

How blockchain-anchored hashes and invisible audio watermarks enable tamper-proof ownership, segment-level verification, and smart-contract licensing on platforms.
-
Rotation, Scaling, Translation in Watermarking

How rotation, scaling, and translation break watermarks and the practical defenses—Fourier‑Mellin, log-polar mapping, templates, wavelets, and AI resynchronization.
-
AI Watermarking vs Machine Learning Attacks

Explains how AI watermarks work, why ML attacks can remove or spoof them, and which layered defenses (cryptography, adversarial testing, blockchain) help.
-
Fragile Watermarking in Blockchain-Based Systems

Two-layer system embeds fragile, invisible watermarks and records SHA-256 hashes on blockchain and IPFS to detect any image tampering and automate verification.
